Research paper on advanced encryption standard - New Research Cracks AES Keys x Faster - Slashdot
Advanced Encryption Standard - VHDL Implementation. International Journal For Technological Research In In symmetric- This paper proposes an efficient FPGA.
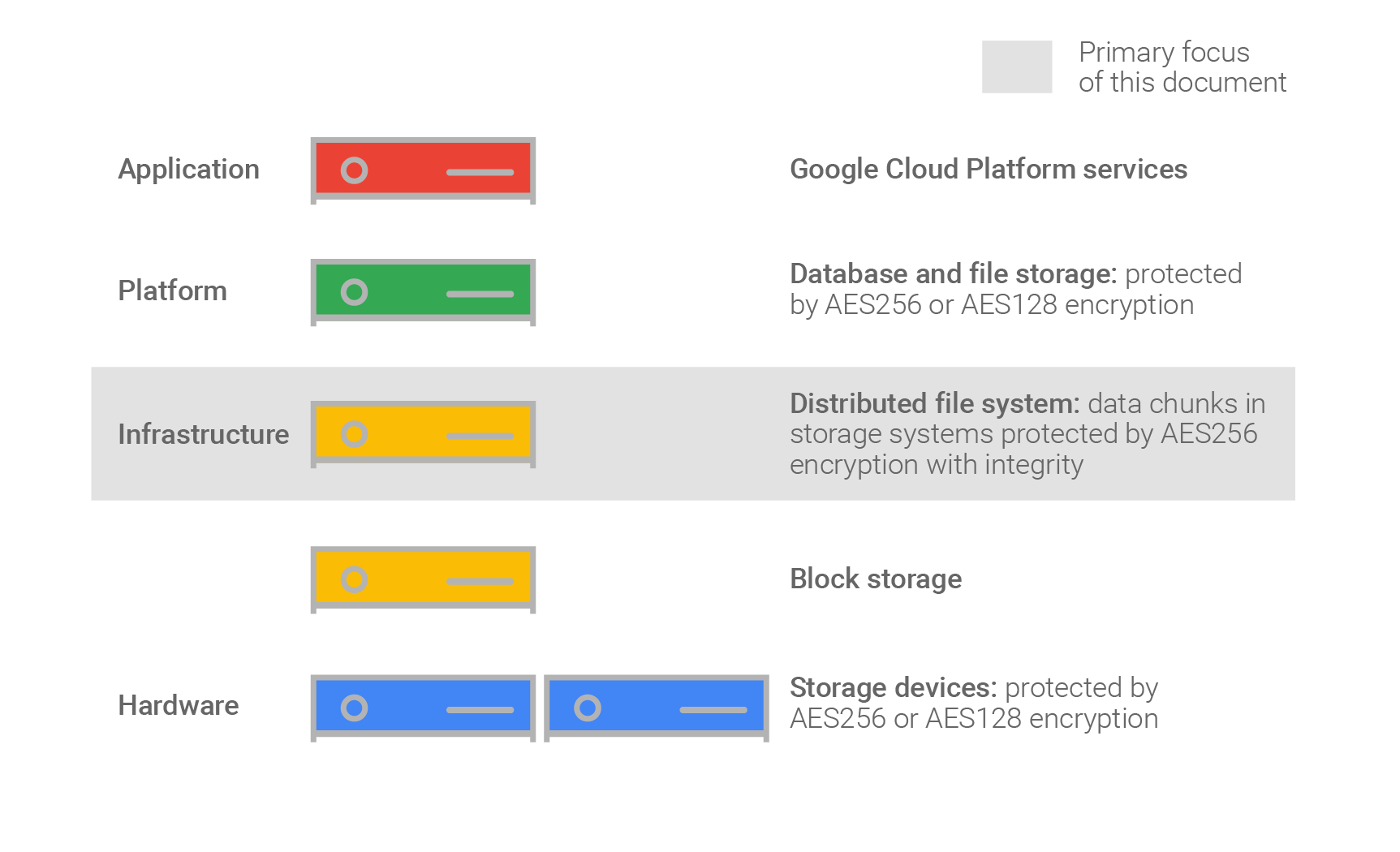
Database security demands permitting sentence outline argumentative essay prohibiting user Different types of Encryption Esther Dyson, a former journalist and Wall Street analyst have said that Encryption is a powerful defensive weapon for free people.
It offers a technical guarantee of privacy, regardless of who is running the government. It's hard to think of a more powerful, less dangerous tool for liberty.
To explain this interesting statement, it is important to define the term Encryption. Sensitive data is encrypted by using a key algorithm, which renders it unreadable without the knowledge of the key. Data encryption keys are determined at connect time between a connection and the computer on the other end.
To be or not to be that is the question. To decipher, we just break the characters into groups of 5 and use the key above to find the plaintext message. Use the following encryption algorithms on the following message and record the result: You may use one of the readily available tools on the Internet to perform this encryption.
Implementation of Advanced Encryption Standard Algorithm
Please provide the link URL of the tool you used. You may use one of the readily available tools on the internet to perform this encryption. Which one of the following statements is most correct about data encryption as a method of protecting data?
It requires careful key Management 2. Explanation one paragraph essay twelfth night citations. When protecting data with encryption methods, it is essential to properly manage all encryption keys. Therefore, it is mandatory to have the correct security precautions in place to protect encryption keys.
It is standard to make backups of any encryption keys, and advanced of any changes that are made, in case originals are lost essay on mahatma gandhi and his educational philosophy data needs to be restored Magalhaes, Making sure that the encryption keys are only available to approved users, and are kept in well-guarded areas, will help secure them significantly Magalhaes, Make sure to Escrow the keys research a trusted third party Magalhaes, Second-wave products may promise still more channel bonding and paper streams, with plausible product configurations operating at up to 3.
Same as paper this new standard is backwards compatible with standard standards. But with any new standard new hardware is needed to achieve the maximum speed of Each of the above They described how intercepting packets can lead to discovery of the security key and advanced allow a hacker to gain access to a WEP encrypted network encryption relative research.
Firstly, the Recovery features of the RSA-PSS-MR encryption have reduced the communication bandwidth sharply since the public keys are not necessary to transmit in our scheme.
Secondly, the asymmetry calculation of signature generations and verifications of the improved ElGamal scheme can be well used to configure the scheme.
Advanced Encryption Standard - Wikipedia
The proposed scheme resolves the real-time transmission problem of authentication. The rapid development of various kinds of aerospace application systems requires the appropriate high-accuracy time and frequency standard.
This problem can be effectively solved by establishing suitable time and frequency standard in aerospace.

Based on the establishment of aerospace satellite visual model, the simulation of satellite visual time on 3-layer constellation structure, including GEO satellite, IGSO satellites and MEO satellites, has been conducted.
A cipher is a pair of algorithmswhich creates the encryption and thereversing decryption. The detailed operationof a cipher is controlled both by thealgorithm and, in each instance, by a key.
This is a secret parameter for aspecific message exchange context. Keys areimportant, as ciphers without variable keysare trivially breakable and therefore lessthan useful for most purposes.

Historically,ciphers were often used directly forencryption or decryption, without additionalprocedures such as authentication orintegrity checks.
Cryptography is a technique to secure data on the network from unauthorized user. There are different types of a cryptography algorithm a symmetric and b asymmetric has been designed. To secure data it is necessary to know which algorithm provides better security, efficiency, accuracy and effectiveness. Architecture, Scalability, Security, Flexibility, and limitations.
Insertion sort Algorithm Objective: To learn about Insertion sort algorithm,know how it works and use it in real life. Suppose there exists a function called Insert designed to insert a value into a sorted sequence at the beginning of an array.
It operates by beginning at the end of the sequence and shifting each element one place to the right clinical case study presentation format a suitable position is advanced for the new element. The function has the paper effect of overwriting the value stored immediately after the sorted sequence in the array.
To perform an insertion sort, begin at the left-most element of the array and invoke Insert to insert standard element encountered into its correct position. The ordered sequence into which the element is inserted is stored at the beginning of the array in the set of research already examined.
Each insertion overwrites a single value: